“AI will revolutionize every aspect of connectivity,” was the bold message delivered during a recent webinar by the IDC titled ‘AI with everything – the future of Artificial Intelligence in Networking.‘
The synopsis of the webinar argued that artificial intelligence (AI) is changing how networks are built and operated in the most profound of ways. Additionally, IT professionals are more reliant than ever on networks to keep enterprises agile, secure and competitive. As a result, advanced tools are needed to keep networks running at optimal levels. AI plays a critical part in making network operations simpler, smarter, more secure and faster.
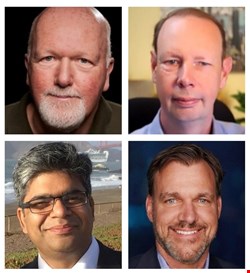
The webinar was led by Mark Leary, research director for network analytics and automation at the IDC. Joining him were Andrew Coward, GM, software defined networking, at IBM; Kevin Deierling, senior vice president of NVIDIA; and Gaurav Rastogi, senior director, R&D, of VMware.
AI-Driven Changes
The webinar opened with the rousing claim by Leary that AI-driven change is needed if mounting network challenges are to be addressed: ”The recent Google Cloud outage is still being investigated, but it was identified as a networking issue.”
“The Facebook problem a month ago, same thing, another networking matter. We’ve seen a wealth of these problems over the last few years. This is Facebook, Google, AWS, people with a lot of sophisticated expertise available to them. Yet, they’re having trouble with the complexity that networks present to them.”
Leary warned that the pressures on network professionals are building, with network professionals experiencing new challenges. Additionally, they recognize the need to make networks not just better but simpler: “For that, we really have to turn to smarter systems that are driven by AI and machine learning,” he contended.
Yet, it’s crucial to get a good understanding of what you want from AI, emphasized Leary. “IT and network automation is a top concern for senior execs.” He added that ”It’s a tremendous opportunity for AI to bring its smarts, not only in areas like development and governance but also the triggering of automated events and directing of automated activities.”
“AI offers a more dynamic network infrastructure,” he explained. ”One that’s easier to manage, that’s more secure and that is better at adapting to requirements as they develop.
“It’s about trying to figure out how to get better at delivering a truly resilient infrastructure. Whether you’re small, medium or large, AI should be infused within your IT infrastructure. AI infusion is something that you don’t really see, but you realize the benefits soon enough.”
AI Trends
With the conversation shifting to the trends industry leaders are noting, Coward remarked that he sees customers shifting towards network data gathering from disparate sources, such as WiFi or the wide area network and even the cloud. However, “they find they can’t quickly solve problems,” he said. “The paradox is that the more information they’ve collected, the less clarity they seem to get. Attention is now switching to how to use AI to separate out the noise and focus on what’s the real problem.”
Deierling commented that enterprises want to be able to operationalize data by using machine learning to “write a program that can then do inferencing to guide activities.”
“We’re seeing the atomization of the network, the breaking up of monolithic applications and the rise of containerized microservices. The impact is massive,” he said. “Suddenly, you’ve got a thousand times more east-west traffic inside of the network. Instead of being embedded into a single software program, you have connections between all these micro services and the zero trust environment.”
Deierling also highlighted the role AI can play in natural language processing: “All of that is incredibly dependent on the network. For someone to engage with an AI device and get human response times means that the network needs to be operating flawlessly. It all has to happen in real time, and there’s so much data being processed.”
AI: Worries and Solutions
However, AI is not a silver bullet, warned Rastogi, and we shouldn’t discount the human element: “When decisions are built on AI, there will be false positives,” he warned. Therefore, the efficacy of what AI is doing needs to be measured.
“AI will never be black and white or offer 100% accuracy in decisions. There will always be times when it can be wrong and humans need to come in and help that out. Decisions must be in tune with what security or network admin intuition says.”
This issue is increasingly addressed, replied Coward, who has seen organizations develop digital twins to test out what changes to their infrastructure might mean. “If the digital twin survives, then you know that you’re probably in a good place to post that to the rest of the network,” he explains. “There are some interesting ways of understanding a new model.”

Concerning AI and networking, many enterprises are undervaluing the possibilities available to them, fears Deierling: “I think that AI is going to be much bigger than people realize…it’s the most powerful technology force of our time. Companies that realize that and embrace AI and infuse it into their businesses are going to succeed, and companies that don’t are going to fall behind. I think in five years, or a decade, every business will be an AI business.”
Concerning concepts like digital twin, Deierling mentioned that people should consider its significance: “I don’t think people understand how large the virtual world is going to be. It’s much larger than the real world. We just announced a digital twin of Earth. People will define and build products in the virtual world. The key is to fail fast in the virtual world so that you can succeed in the real world
“This is one of the ways in which AI is going to transform businesses. After all, you wouldn’t build a car or a plane without simulating. In data science, people will build a digital twin using AI to detect anomalous behavior and network hotspots; everything modeled accurately and precisely.”
Rastogi noted the importance of simplicity and automation in customer decisions: “They are expecting systems to take care of the fine-tuning. That is not going to be possible without AI. AI is going to be a core piece of how to figure out what is your baseline what are the optimizations in the system.”
AI and Security
Security is another benefit of AI implementation, he added. “Web application attacks are on the rise…The attack vectors you see are like 70% to do with credentials and 30% about misconfigurations. AI will build out solutions to protect web applications, protect the network and figure out if there is malware installed.”
In conclusion, Deierling stressed the importance of having a secure framework upon which to build any AI application. He gave the example of 5G: “We see a ton of use cases where people are using AI-enabled 5G for robotics and smart factories, and you need low latency and slicing for that. If you have a real platform that does 5G, then it really supports all those AI workloads whether that’s a kiosk in an airport that’s using natural language processing or avatars and visual analytics.”
