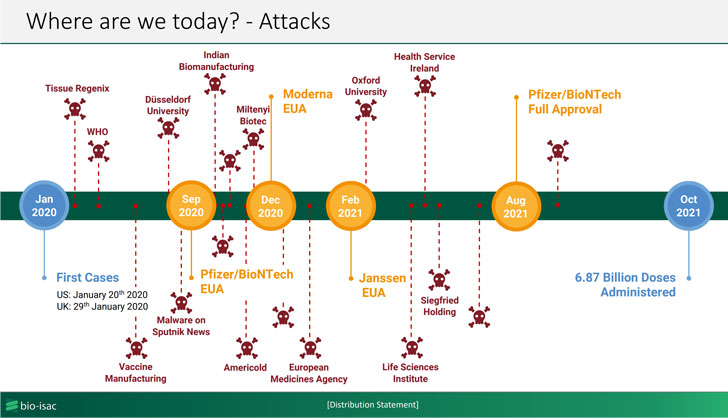
An advanced persistent threat (APT) has been linked to cyberattacks on two biomanufacturing companies that occurred this year with the help of a custom malware loader called “Tardigrade.”
That’s according to an advisory published by Bioeconomy Information Sharing and Analysis Center (BIO-ISAC) this week, which noted that the malware is actively spreading across the sector with the likely goal of perpetrating intellectual property theft, maintaining persistence for extended periods of time, and infecting the systems with ransomware.
BIO-ISAC, which commenced an investigation following a ransomware attack targeting an unnamed biomanufacturing facility earlier this spring, characterized Tardigrade as a sophisticated piece of malware with “a high degree of autonomy as well as metamorphic capabilities.” The same malware was then used to strike a second entity in October 2021.
The “actively spreading” intrusions have not been attributed to a specific threat actor or a nation, but the agency told The Hill that the efforts mirrored previous attacks by a hacking group linked to Russia.
Spread via phishing emails or infected USB drives, Tardigrade is an advanced offshoot of SmokeLoader, a Windows-based backdoor operated by a group known as Smoky Spider and available for sale on underground markets dating all the way back to 2011, with the former possessing capabilities to capture keystrokes, laterally move across the compromised network, and escalate privileges.
What’s more, the malware acts as an entry point for additional malware payloads and is engineered to operate autonomously even when cut off from its command-and-control server to carry out its malicious activities. Organizations in the biomanufacturing industry are advised to apply software updates, enforce network segmentation, and test offline backups of critical biological infrastructure to mitigate the threats.
“This malware is extremely difficult to detect due to metamorphic behavior. Vigilance on key personnel corporate computers is important,” the researchers said, adding “Many machines in the sector use outdated operating systems. Segment them off aggressively and accelerate upgrade timelines.”