A Pakistani threat actor successfully socially engineered a number of ministries in Afghanistan and a shared government computer in India to steal sensitive Google, Twitter, and Facebook credentials from its targets and stealthily obtain access to government portals.
Malwarebytes’ latest findings go into detail about the new tactics and tools adopted by the APT group known as SideCopy, which is so-called because of its attempts to mimic the infection chains associated with another group tracked as SideWinder and mislead attribution.
“The lures used by SideCopy APT are usually archive files that have embedded one of these files: LNK, Microsoft Publisher or Trojanized Applications,” Malwarebytes researcher Hossein Jazi said, adding the embedded files are tailored to target government and military officials based in Afghanistan and India.
The revelation comes close on the heels of disclosures that Meta took steps to block malicious activities carried out by the group on its platform by using romantic lures to compromise individuals with ties to the Afghan government, military, and law enforcement in Kabul.
Some of the prominent attacks were waged against personnel associated with the Administration Office of the President (AOP) of Afghanistan as well as the Ministry of Foreign affairs, Ministry of Finance, and the National Procurement Authority, resulting in the theft of social media passwords and password-protected documents. SideCopy also broke into a shared computer in India and harvested credentials from government and education services.
In addition, the actor is said to have siphoned several Microsoft Office documents, including names, numbers, and email addresses of officials and databases containing information related to identity cards, diplomatic visas, and asset registrations from the Afghani government websites, all of which are expected to be used as future decoys or to fuel further attacks against the individuals themselves.
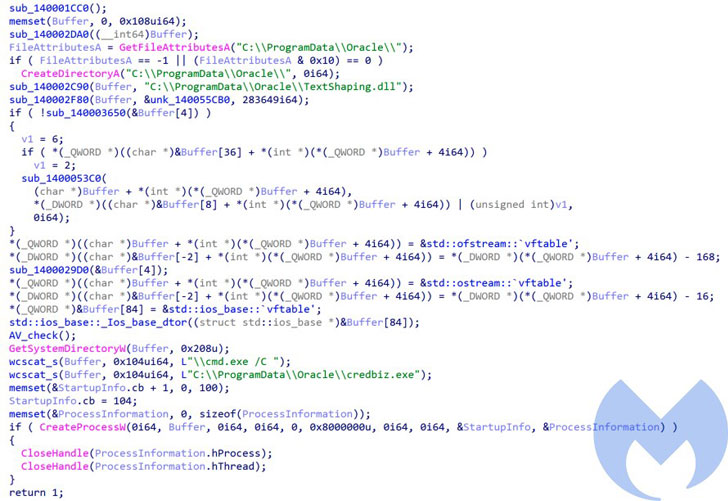
The cyber espionage campaign observed by Malwarebytes involves the target opening the lure document, leading to the execution of a loader that’s used to drop a next-stage remote access trojan called ActionRAT, which is capable of uploading files, executing commands received from a server, and even download more payloads.
Also dropped by the loader is a new information stealer dubbed AuTo Stealer, which is programmed to collect Microsoft Office files, PDF documents, text files, database files, and images before exfiltrating the information to its server over HTTP or TCP.
This is far from the first time SideCopy APT’s tactics have come to light. In September 2020, cybersecurity firm Quick Heal revealed specifics about an espionage attack aimed at Indian defense units and armed forces personnel at least since 2019 with an aim to steal sensitive information.
Then earlier this July, Cisco Talos researchers exposed the hacking group’s myriad infection chains delivering bespoke and commodity remote access trojans such as CetaRAT, Allakore, and njRAT in what they called an expansion of malware campaigns targeting entities in India.