A Rust variant of a ransomware strain known as Agenda has been observed in the wild, making it the latest malware to adopt the cross-platform programming language after BlackCat, Hive, Luna, and RansomExx.
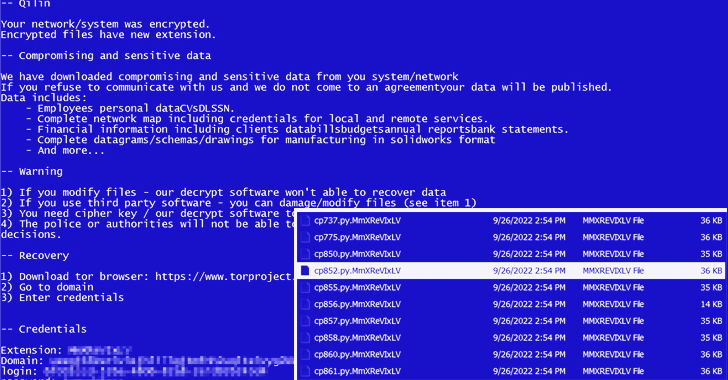
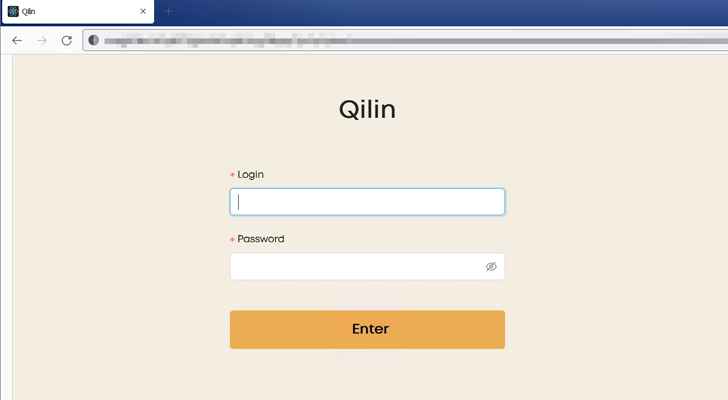
Agenda, attributed to an operator named Qilin, is a ransomware-as-a-service (RaaS) group that has been linked to a spate of attacks primarily targeting manufacturing and IT industries across different countries.
A previous version of the ransomware, written in Go and customized for each victim, singled out healthcare and education sectors in countries like Indonesia, Saudi Arabia, South Africa, and Thailand.
Agenda, like Royal ransomware, expands on the idea of partial encryption (aka intermittent encryption) by configuring parameters that are used to determine the percentage of file content to be encrypted.
“This tactic is becoming more popular among ransomware actors as it lets them encrypt faster and avoid detections that heavily rely on read/write file operations,” a group of researchers from Trend Micro said in a report last week.
An analysis of the ransomware binary reveals that encrypted files are given the extension “MmXReVIxLV,” before proceeding to drop the ransom note in every directory.
In addition, the Rust version of Agenda is capable of terminating the Windows AppInfo process and disabling User Account Control (UAC), the latter of which helps mitigate the impact of malware by requiring administrative access to launch a program or task.
“At present, its threat actors appear to be migrating their ransomware code to Rust as recent samples still lack some features seen in the original binaries written in the Golang variant of the ransomware,” the researchers noted.
“Rust language is becoming more popular among threat actors as it is more difficult to analyze and has a lower detection rate by antivirus engines.”